
Rubis Photo Gallery Photographs of the Free French Naval Forces submarine Rubis and her crew.
Rubis in Action (Google Map) The map shows the positions of all of Rubis's documented actions.
Rubis Today (Diving Videos) Rubis was scuttled in 1957 off St. Tropez, France, for sonar target practice.
Tribute to Submarines By Winston Spencer Churchill, Prime Minister.
Estuary Panorama (Scrollable Panorama) of the Tay Estuary with wartime points of interest highlighted.
ENIGMA Intelligence and Dundee’s War
Dundee’s connection with modern decryption goes back to Sir Alfred Ewing, the Dundee High School Former Pupil and scientist who led Room 40, the Admiralty’s decryption service in the First World War.
It was signals intelligence gained by Room 40 that led directly to the Battle of Jutland and it was one of Ewing’s team who decoded the infamous Zimmerman Telegram which outlined a plan to draw Mexico into the war on the German side, thus keeping the Americans involved in their own back yard rather than in Europe.
The release of the telegram had the opposite effect as the US declared war on Germany a few days later in 1917.
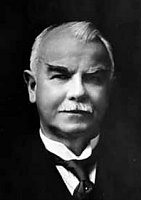
Sir James Alfred Ewing KCB (27th March 1855 – 7th January 1935) was a Scottish physicist and engineer, best known for his work on the magnetic properties of metals and, in particular, for his discovery of, and coinage of the word, hysteresis.
Born in Dundee, Scotland, the third son of a minister of the Free Church of Scotland and educated at West End Academy and the High School of Dundee, Sir James Alfred Ewing showed an early interest in science and technology.
In 1903, he became director of naval education at the Admiralty before becoming principal and vice-chancellor of the University of Edinburgh in 1916, a post he held until his retirement in 1929. From 1914 to May 1917, he managed Room 40, the admiralty intelligence department of cryptanalysis, responsible predominantly for the decryption of intercepted German naval messages.

In the history of cryptography, Room 40 was the section in the Admiralty most identified with the British cryptography effort during World War I.
Room 40 played an important role in several naval engagements during the war, notably in detecting major German sorties into the North Sea that led to the battles of Dogger Bank and Jutland as the British fleet was sent out to intercept them. However its most important contribution was probably in decrypting the Zimmermann Telegram, a cable from the German Foreign Office sent via Washington to its ambassador Heinrich von Eckardt in Mexico.
In the cable’s plaintext, Nigel de Grey and William Montgomery discovered German Foreign Minister Arthur Zimmermann making an offer to Mexico of United States territory as an enticement to join the war as a German ally. The cable was passed to the U.S. by Captain Hall, and a scheme was devised to conceal how its plaintext had become available and also how the U.S. had gained possession of a copy. The cable was made public by the U.S., who shortly thereafter entered the war on the Allied side.
In 1919, Room 40 was run down and merged with the British Army’s intelligence unit MI1b to form the Government Code and Cypher School (GCCS), later housed at Bletchley Park during World War II and subsequently renamed Government Communications Headquarters (GCHQ) and relocated to Cheltenham.
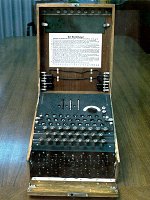
An Enigma machine is any one of a family of related electro-mechanical rotor machines used for the encryption and decryption of secret messages. A range of Enigma models were produced, but the German military model, the Wehrmacht Enigma, is the version most commonly discussed.
The machine has become well-known because Allied codebreakers were able to decrypt a vast number of messages which had been enciphered using the Enigma. The intelligence gleaned from this source, codenamed ULTRA by the British, was a substantial aid to the Allied war effort.
The exact influence of ULTRA is debated, but an oft-repeated assessment is that decryption of German ciphers hastened the end of the European war by two years.
Though the Enigma cipher had cryptographic weaknesses, in practice it was only in combination with other factors (procedural flaws, operator mistakes, occasional captured hardware and key tables, etc.) that those weaknesses allowed Allied cryptographers to cryptanalyze so many messages.